Content of blog
- Why Data Security Matters in Back Office Outsourcing
- Common Threats to Data Security in Outsourcing
- Cybersecurity Threats Businesses Should Watch Out For
- Insider Risks and How to Mitigate Them
- The Cost of Ignoring Data Security in Outsourcing
- Best Practices for Ensuring Data Security in Outsourcing
- Encrypting Data for Maximum Protection
- Role of Multi-Factor Authentication in Securing Data
- Regular Audits and Monitoring for Compliance
- Safeguarding Data Transfers and Communication
- Partnering with Certified Providers
- Compliance Standards for Secure Back-Office Outsourcing
- Key Certifications to Look for in a Provider
- Understanding Regulatory Requirements
- Ensuring Adherence to Industry-Specific Standards
- How ProcessVenue Can Help Secure Your Back Office Operations
- Conclusion: Building a Secure and Efficient Back Office
When outsourcing back-office operations, data security should be a top priority. It involves protecting sensitive information from breaches, ensuring compliance with industry regulations, and mitigating risks associated with third-party access to your data.
To safeguard their operations, businesses must carefully evaluate their outsourcing partners, establish strong data protection policies, and continuously monitor security practices. Read on to learn more!
Why Data Security Matters in Back Office Outsourcing
Without proper security, businesses risk exposing customer data, facing legal penalties, and damaging their reputation. Companies can mitigate the risks of cybersecurity threats and insider breaches by maintaining strong data protection policies and implementing data security best practices.
Common Threats to Data Security in Outsourcing
When you choose BPO outsourcing for your business, you must remain vigilant about potential security risks. Data security threats are common in outsourcing relationships and can result in major financial and reputational damage. So, here are some of the most prevalent risks you should be aware of and how to protect your business from them.
Cybersecurity Threats Businesses Should Watch Out For
Cybersecurity threats in outsourcing are one of the biggest concerns for any business. These threats include hacking, malware, and phishing attacks, which can lead to a data breach. With BPO services often handling sensitive information, hackers may target these outsourced processes.
You should have strong network defenses, encrypted communication channels, and frequent security updates to secure your data. To mitigate such risks, ensure the tour provider follows strict data security policies.
Insider Risks and How to Mitigate Them
Insider threats are another major concern. Employees within the outsourcing company can intentionally or unintentionally cause data leaks or security breaches. Identity and access management (IAM) solutions help you control who has access to sensitive information and prevent unauthorized access.
Proper employee training on data security best practices and monitoring internal activities can reduce the likelihood of these threats. By working closely with your solution provider, you can also ensure they implement strong background checks for their staff.
The Cost of Ignoring Data Security in Outsourcing
Failing to prioritize data protection policy can result in financial and reputational costs. A security breach can lead to lawsuits, penalties, and loss of customer trust, especially if it affects the financial services outsourcing sector.
Additionally, customers expect their data to be handled securely, and failing to meet their expectations could damage your brand. While ignoring data security might initially save you money, the long-term risks can far outweigh any short-term savings.
Best Practices for Ensuring Data Security in Outsourcing
Protecting your data should be a top priority when outsourcing business processes, especially in areas like financial services. Proper data security measures are essential to prevent breaches, meet compliance standards, and safeguard sensitive information. Below are some key data security best practices to follow when outsourcing.

Encrypting Data for Maximum Protection
Encryption is one of the most effective ways to secure your data. By converting sensitive data into unreadable formats, you protect it from unauthorized access. Whether your data is at rest (stored data) or in transit (data being transferred), encryption is critical to keeping it safe from external threats and unauthorized personnel.
Role of Multi-Factor Authentication in Securing Data
Multi-factor authentication (MFA) adds an extra layer of security by needing more than a password to access systems or data. With MFA, users must provide additional verification, such as a code sent to their phone or a fingerprint scan. This lowers the risk of unauthorized access, especially during financial services outsourcing, where sensitive customer data must be protected.
Regular Audits and Monitoring for Compliance
Regular security audits and continuous monitoring are necessary to comply with data protection policies and regulatory standards. These include checking for vulnerabilities, ensuring all systems are up to date, and reviewing access logs. Regular checks help identify and fix potential security gaps before they become threats, which is especially important in cybersecurity threats in outsourcing environments.
Safeguarding Data Transfers and Communication
When transferring data between systems or over the Internet, use secure channels, such as Virtual Private Networks (VPNs) or encrypted connections (SSL/TLS). Data security policies should dictate secure communication and data-sharing methods to prevent breaches during transit. Safeguarding these transfers to protect against interception or leaks is essential.
Partnering with Certified Providers
Choose BPO service providers certified in data security standards, such as ISO 27001. These certifications indicate that a provider follows strict security practices to protect your data. Partnering with trusted and certified providers will help you mitigate risks and avoid potential liabilities related to reducing security vulnerabilities and protecting financial industry data.
Compliance Standards for Secure Back-Office Outsourcing
By choosing a provider that follows the right security certifications and guidelines, you can better protect sensitive data, reduce risks, and remain compliant with relevant laws. Below are key points to consider when evaluating the compliance standards for secure outsourcing:
Key Certifications to Look for in a Provider
Look for BPO service providers certified in established security standards, such as the International Organization for Standardization (ISO) 27001 and System and Organization Controls (SOC 2).
These certifications indicate that the provider follows strict practices for handling and securing data. Also, certifications related to data security policies and compliance show the provider’s commitment to safeguarding your information.
Understanding Regulatory Requirements
Depending on the industry, specific regulations may apply to handling sensitive data. For example, financial services outsourcing requires compliance with laws such as KYC compliance, ensuring companies verify clients’ identities to prevent fraud.
Ensuring Adherence to Industry-Specific Standards
Certain industries like healthcare or finance have more stringent data protection requirements. The provider should adhere to industry-specific standards, such as HIPAA (Health Insurance Portability and Accountability Act) for healthcare or the Payment Card Industry Data Security Standard (PCI-DSS) for payment processing.
Adhering to these regulations helps you secure your data, prevent breaches, and reduce security vulnerabilities related to industry-specific threats.
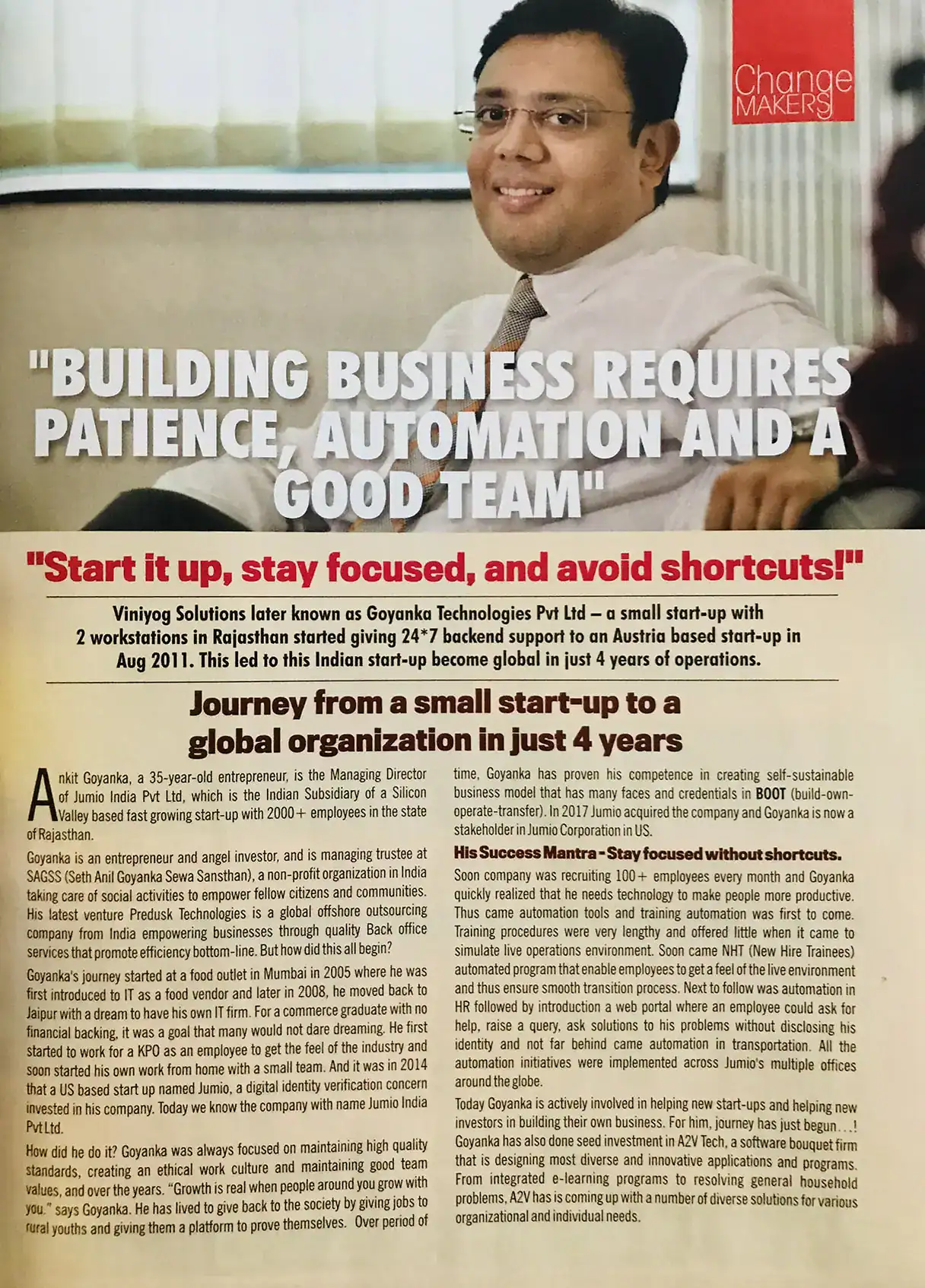
How ProcessVenue Can Help Secure Your Back Office Operations
ProcessVenue offers robust solutions to secure your data and protect your back-office operations. With a focus on data security, we implement strict data security policies, including encryption, multi-factor authentication, and continuous monitoring to guard against cybersecurity threats in outsourcing.
Our experienced team helps you navigate compliance requirements and mitigate insider risks with strong identity and access management practices. By partnering with ProcessVenue, you can ensure that your back-office operations are safeguarded against data breaches while maintaining operational efficiency.
Conclusion: Building a Secure and Efficient Back Office
In conclusion, keeping your data secure is non-negotiable when outsourcing. By partnering with a reliable provider like ProcessVenue, you can safeguard your data through robust security practices, ensuring your operations remain secure and compliant.